IOS 14 added a new sandbox security system “BlastDoor” for iPhones and iPads to prevent attacks carried out with the Messages app. Apple did not share information about the new security addition, but it was explained today by Samuel Groß, a security researcher at Google Project Zero, and highlighted by ZDNet.
/article-new/2020/06/messages-pinned-conversations-ios-14.jpg?resize=560%2C410&ssl=1)
Groß describes BlastDoor as a totally secure service that is responsible for analyzing all unreliable data in iMessages. A sandbox is a security service that runs code separately from the operating system, and it operates within the Messaging application.
BlastDoor analyzes all incoming messages and inspects their content in a secure environment, which prevents any malicious code within a message from interacting with iOS or accessing user data.
/article-new/2021/01/project-zero-blastdoor.jpg?resize=560%2C458&ssl=1)
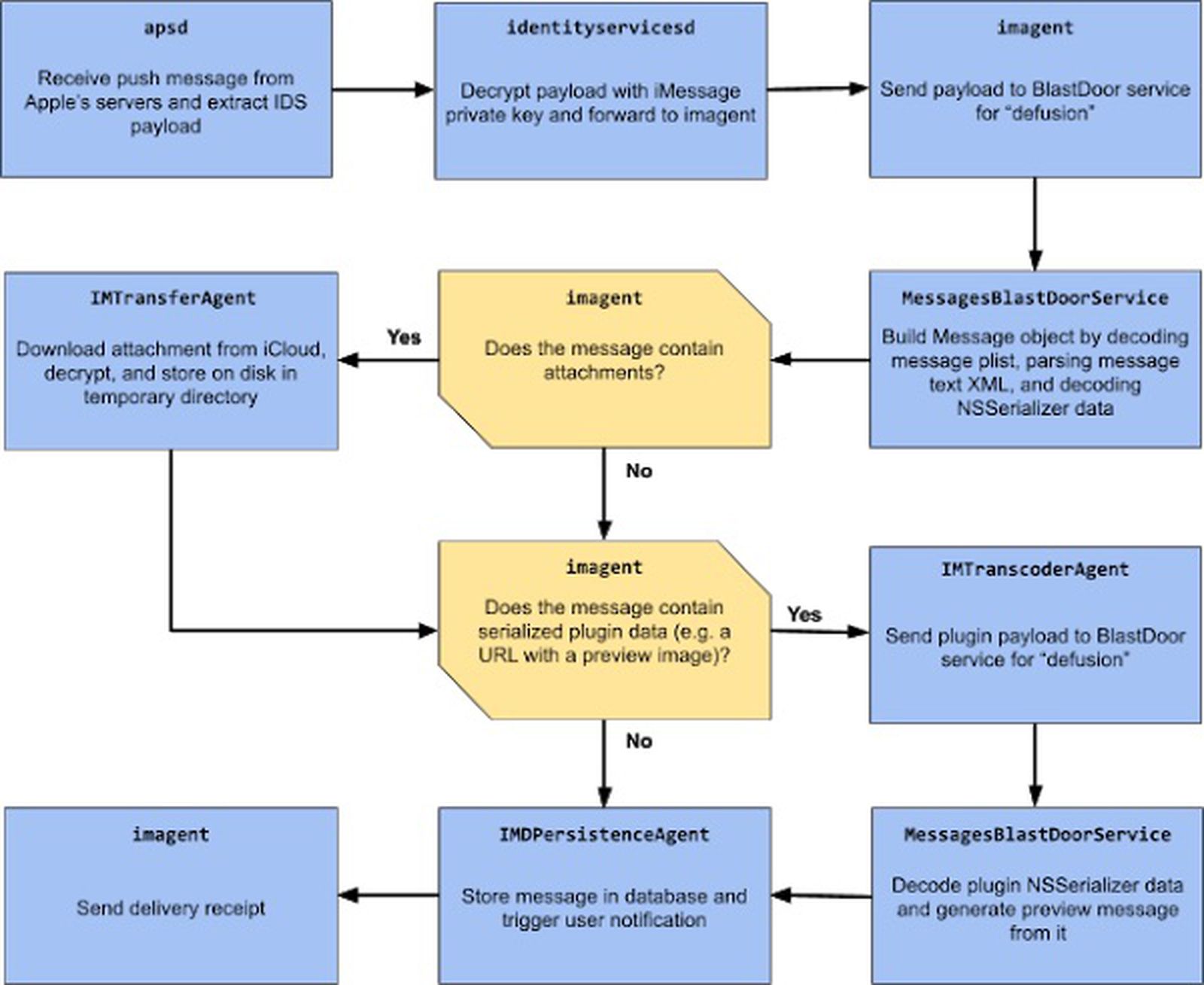
As can be seen, most of the complex and unreliable data processing has been moved to the new BlastDoor service. In addition, this project with its 7 + services involved allows fine-grained sandbox rules to be applied, for example, only the IMTransferAgent and apsd processes are needed to perform network operations. As such, all services in this pipeline are now properly sandboxed (with the BlastDoor service arguably the strongest in sandbox).
The feature was designed to prevent specific types of attacks, such as those where hackers used shared caching or brute force attacks. Like ZDNet points out, security researchers have found bugs in remote iMessage code execution in recent years that could allow an iPhone to be infiltrated with just one text, which BlastDoor must resolve.
Groß found the new feature iOS 14 after investigating a Message hacking campaign that targeted Al Jazeera journalists. The attack was not working on iOS 14 and the investigation of the reason led to the discovery of BlastDoor.
According to Groß, changes to Apple’s BlastDoor are “close to the best that could have been done, given the need for backward compatibility”, and will make the iMessage platform significantly more secure.
This blog post discussed three improvements in iOS 14 that affect iMessage security: the BlastDoor service, shared cache resliding and exponential limitation. Overall, these changes are probably very close to the best that could have been done, given the need for backward compatibility, and should have a significant impact on the security of iMessage and the platform as a whole.
It’s great to see Apple reserving resources for these types of major refactorings to improve the safety of end users. In addition, these changes also highlight the value of offensive security work: not only have single bugs been fixed, but instead, structural improvements have been made based on insights gained from exploit development work.
Those interested in knowing how BlastDoor works can visit the Project Zero blog post on the subject.